Identity / Zero Trust
IAM and Zero Trust: Identity-First Security Architecture for Modern Systems
Zero Trust increasingly depends on identity and access management to verify users, govern access, reduce privilege, and make trust decisions more explicit. This hub explores Zero Trust IAM, IAM architecture, identity governance, privileged access, authentication design, and the practical foundations of identity-first security.
It is designed as a growing hub for clear, applied thinking on how trust is structured in modern systems and why identity is increasingly the control plane of security architecture.
Featured article

Start here
Identity Is the New Control Plane
A foundational piece on why modern security architecture increasingly starts with identity rather than perimeter assumptions.
Read articleArchitecture diagrams
Architecture diagram
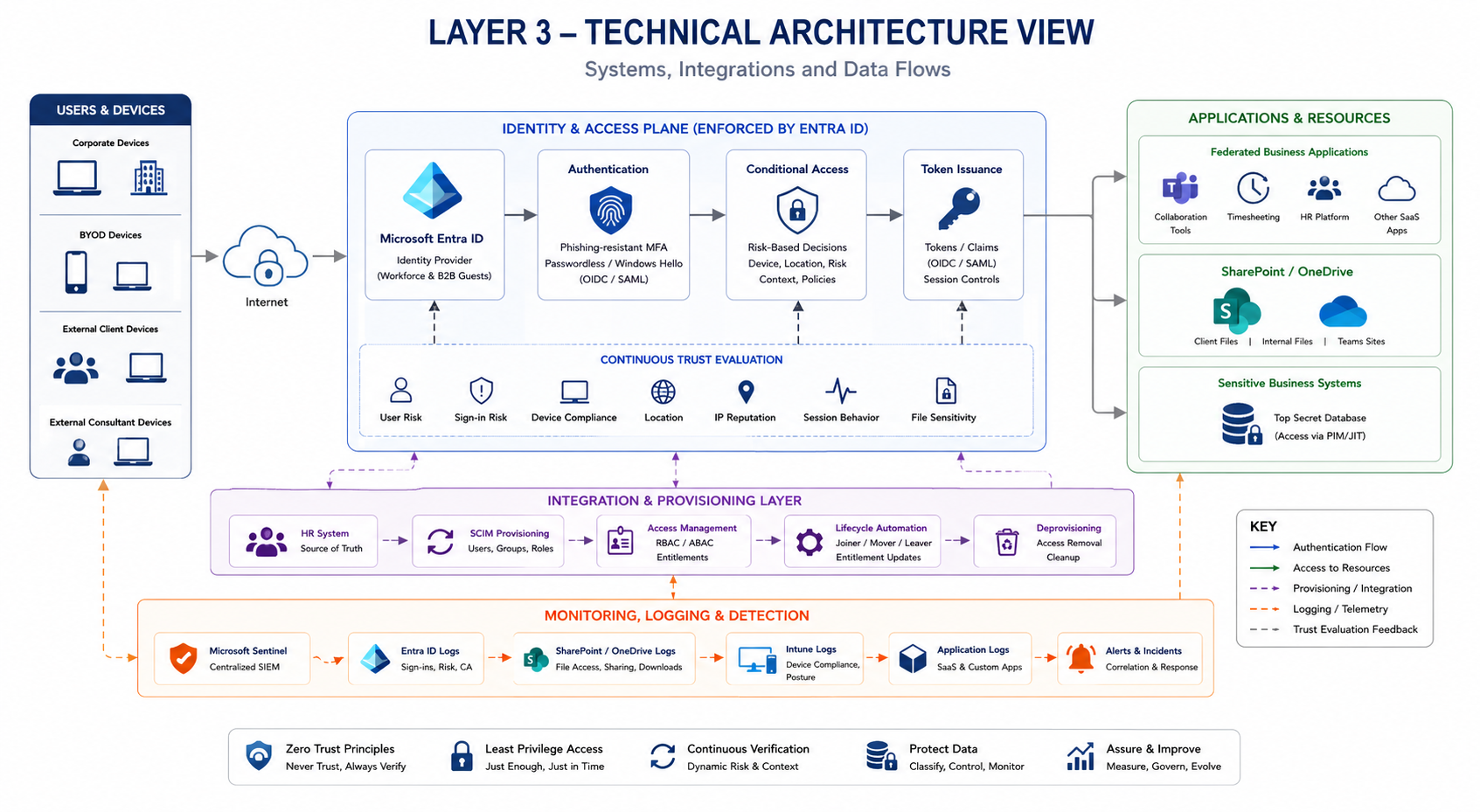
Identity-Centric Zero Trust Architecture for Cloud Consultancies
A practical architecture scenario showing how identity, access decisions, conditional access, privileged access, cloud services, and monitoring work together in a Zero Trust model.
View diagram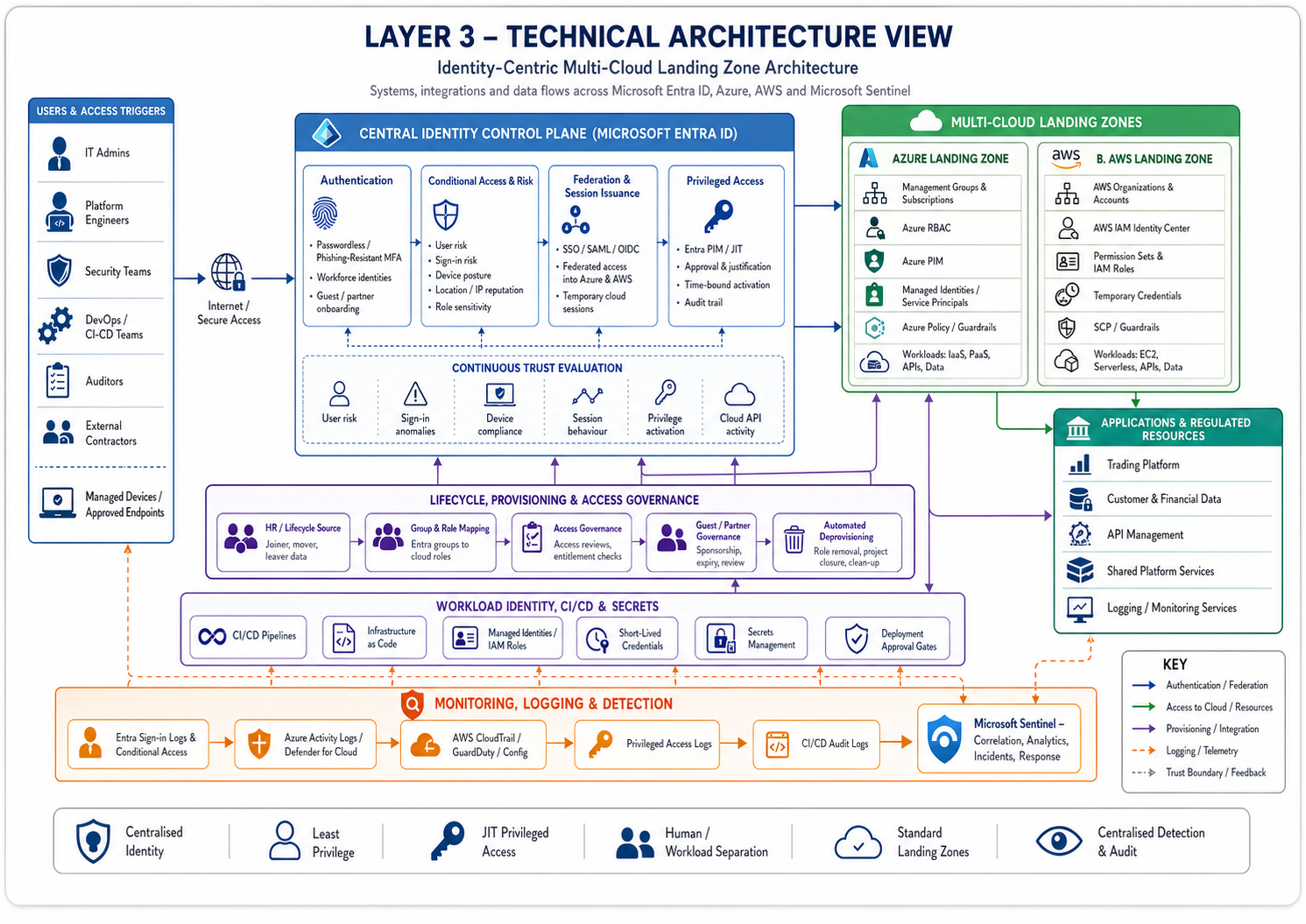
Architecture diagram
Identity-Centric Multi-Cloud Landing Zone Architecture
A regulated fintech reference architecture showing how Microsoft Entra ID, Azure, AWS, privileged access, workload identity, landing zone governance, and Microsoft Sentinel work together in an identity-first multi-cloud model.
View diagramWhat is Zero Trust IAM?
Zero Trust IAM refers to the way identity and access management supports Zero Trust principles in practice. Instead of assuming trust based on network location, organisations verify identity, evaluate access requests more carefully, and apply policy with greater precision. In that model, IAM becomes central to how trust is established, limited, reviewed, and enforced.
In other words, Zero Trust is not just a network idea. It relies heavily on identity to decide who should access what, under which conditions, and with what level of privilege.
Identity and access management architecture principles
- Explicit verification: trust decisions should be based on stronger identity signals, not assumptions.
- Least privilege: users and systems should receive only the access they actually need.
- Lifecycle control: joiners, movers, and leavers must be reflected in access decisions quickly.
- Policy-driven access: access models should be structured, consistent, and increasingly context-aware.
- Privileged access isolation: high-impact access requires stronger control and visibility.
- Auditability: identity decisions should be reviewable, explainable, and traceable.
- Operational maintainability: IAM architecture should support growth without collapsing into access sprawl.
Why identity governance matters in Zero Trust
Identity governance is one of the practical foundations of Zero Trust. Without strong lifecycle control, role clarity, access review, and better visibility over entitlement drift, Zero Trust becomes harder to sustain in practice.
That is why identity governance and Zero Trust are closely linked. Policy can only work well if access is governed cleanly over time.
What this hub covers
- Identity-first architecture and modern trust design
- Zero Trust IAM and how identity supports practical Zero Trust
- IAM architecture and identity and access management architecture principles
- Access control models, including RBAC, ABAC, and policy-driven approaches
- Privileged access and cloud-native access design
- Authentication, tokens, certificate lifecycle, and trust enforcement
- Identity governance, lifecycle control, and access review
- Multi-cloud identity, landing zone governance, and identity-led cloud security
Frequently asked questions
A few of the core questions security teams and architects ask when connecting IAM and Zero Trust.
What is Zero Trust IAM?
Zero Trust IAM refers to the way identity and access management supports Zero Trust by verifying identity, limiting privilege, structuring access decisions, and reducing reliance on implicit trust.
How does IAM support Zero Trust?
IAM supports Zero Trust by helping organisations verify identities, manage access more precisely, reduce excessive privilege, govern lifecycle changes, and apply more consistent policy to trust decisions.
What are identity and access management architecture principles?
Common IAM architecture principles include explicit verification, least privilege, lifecycle control, policy-driven access, privileged access isolation, auditability, and operational maintainability.
Why is identity governance important in Zero Trust?
Identity governance helps keep Zero Trust practical over time by reducing privilege creep, improving lifecycle control, supporting access review, and keeping roles and entitlements more aligned with reality.
When do organisations need stronger IAM architecture?
Stronger IAM architecture becomes more important as systems become more distributed, privileged access grows, lifecycle complexity increases, and identity becomes more central to security and compliance expectations.
